Foros Perspectives occasionally invites senior team members to offer a personal assessment on a topic. This contribution is from our Advisory Director Lonne Jaffe, former CEO of Syncsort.
Google and Amazon: Canaries in the Enterprise Coal Mine
Recent actions by these technology giants foreshadow potential existential threats to many large hardware and software companies that may lead to market consolidation, an increase in divestitures, and even the shuttering of businesses
Last week, Google announced the release of Cloud Spanner, its powerful database platform distributed across millions of machines worldwide. This distributed platform has powered Google services such as Gmail for years, and it’s now available as a service via the cloud for any enterprise to use for less than a dollar per node per hour. In a related announcement, Google published an Infrastructure Security Review explaining the vast scope of the security measures it takes to protect its cloud operations. The document explains the Google designed custom hardware security chip that uses advanced cryptography to securely identify and authenticate legitimate Google-built devices at the hardware level. Snapchat relies on Google secure cloud services and paid Google nearly all of its 2016 revenue to do so, according to its recent IPO filing.
Last week, Amazon also announced its full scale invasion of the Unified Communications (UC) marketplace with Amazon Chime, providing advanced encryption and security capabilities and built on the market-leading Amazon Web Services cloud platform.
It’s not hard to imagine a day when the likes of Google and Amazon will be the only ones with enough security talent and resources to protect companies and consumers from serious cybersecurity threats. When it comes to cyberattacks, governments may not be able to attract and retain the talent needed to protect themselves and their citizens.
Today many believe that traditional on-premise systems, such as the data centers at large banks, are more secure than cloud platforms. However, as companies and governments begin to realize that cloud platforms are more secure – not less secure – than their on-premise counterparts, the already rapid shift from on-premise systems to the public cloud platforms will accelerate. This trend may become an existential threat to legacy enterprise software and hardware vendors, since the public cloud platforms such as Google and Amazon Web Services are building much of the hardware and software they need, not buying it from technology vendors.
This acceleration in the shift to the cloud is compounded by a number of other secular factors that are harmful to traditional infrastructure technology business models. While not a death knell, these threats should be an impetus for a comprehensive strategic and technology assessment including, in extreme circumstances, winding down legacy businesses.
Open Source Matures: First, much of the best enterprise software being used today is available through open source projects such as Apache Hadoop and Apache Kafka that have been created by companies such as Google or LinkedIn for internal use and, then later, released as open source to the world. Partnerships between academia and private companies, such as UC Berkeley’s AMPLab, and its recently announced RISE Lab, have created powerful open source software and hardware projects such as Apache Spark that aren’t owned by a single company. Instead, they are freely shared online and are improving at a more rapid pace than similar products provided by legacy vendors. A number of well-resourced companies, such as Databricks and Confluent, have emerged to provide customers with commercial support around these valuable platforms for a small fee.
Direct to User Marketing: Second, one of the biggest historical barriers to entry in enterprise software and hardware, the need for a large direct sales force with senior relationships with decision makers at enterprise buyers, is eroding. Over the past several years fast-growing companies such as Splunk and Tableau have grown by allowing customers to download their software over the Internet, rapidly becoming multi-billion dollar businesses at the expense of legacy vendors. These two companies, both founded in 2003, grew from $50mm of revenue to nearly $1bn of revenue in just seven years as shown in the chart below.
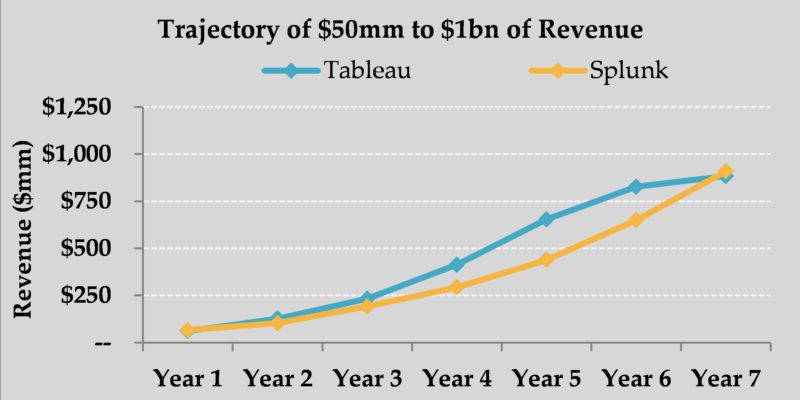
Tableau’s Year 7 revenue represents Wall Street consensus revenue estimate for 2017, per FactSet
Disruption of Value Points: Third, as technology components drop in price, new architectures emerge, and bottlenecks shift. Some previously high-value software is rendered irrelevant. For example, as computer memory prices have dropped dramatically over the last few years, dozens of software products built around the assumption that memory would be expensive have become obsolete.
In the face of these and other threats, legacy enterprise software and hardware vendors should take immediate steps to evaluate their strategic options. The strongest players should seek to roll-up their segments via M&A. Acquiring smaller companies can produce scale economics, cost efficiencies, and high returns on invested capital with less risk than launching new technological initiatives.
Those companies that are not in the position to acquire others have at least two additional options. If the opportunity exists, they should consider selling their legacy software and hardware divisions, or even their whole company. Another approach worth considering is winding down some businesses and returning cash to shareholders. In some cases, winding a business down effectively, if it is in a fundamentally unattractive market over the long-term, can be the best outcome compared to other alternatives.
Complacency by technology companies in the face of these changes is not an option.
